 In 2013, everyone was shocked about the news on the huge Target financial data breach that compromised 110 million of its customers’ credit and debit card numbers, plus their encrypted personal identification numbers. The company had to pay $39-million worth of settlement to appease its affected customers.
In 2013, everyone was shocked about the news on the huge Target financial data breach that compromised 110 million of its customers’ credit and debit card numbers, plus their encrypted personal identification numbers. The company had to pay $39-million worth of settlement to appease its affected customers.
It’s not just big companies that can get into this bad situation. It can happen to any business regardless of size. If yours faces the same challenge, you must know how to get out of it fast.
First thing you have to know: how does a database breach occur? Hackers usually create a malware embedded with a script or code that allows them to gain full access to the system remotely.
Or if they’re hacking the computer on location, they use a command to gain administrative access to the system, and then get the credit card application files of everyone in the database.
Here are the two most common types of cybercrimes that can threaten financial data security:
Ransomware Attacks
Ransomware is distributed as a nondescript Word document that is passed through email. Once the document is opened, it automatically encrypts your tax data and demands for a certain amount of money as a sort of ransom to unlock the said files. It usually attacks files with .tax2013 and .tax2014 extensions used by tax management tools.
Banking Credentials Theft
This type of cybercrime involves phishers getting your banking details through a fake website that mimics your banking website’s log-in page.
Scammers can also do this through a malware that crawls through your online banking app to retrieve sensitive information from your phone without your knowledge.
Ways to Recover from a Financial Security Breach
- Hire a professional to fix the damage.
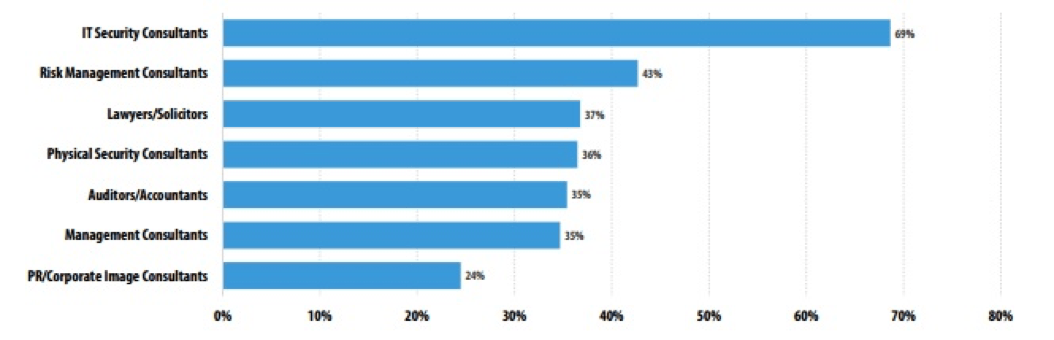
Image Source: Kaspersky Lab’s Damage Control: The Cost of Security Breaches IT Security Risks Special Report Series
According to the data above, a company usually hires the following professionals to alleviate the damage caused by financial security breaches:
- IT security consultants manage the damage done to the hacked system and prevent similar instances from happening in the future through stronger defense.
- Risk management consultants and lawyers help with solving specific problems caused by security breach incidents.
- Auditors/Accountants calculate the loss and the damages the company needs to pay to each affected client or employee.
- PR consultants help manage a brand’s or company’s reputation. If you have a more personal financial security breach concern, you can use an online reputation management site like MyLife to clean up your brand’s online presence.
- Management consultants help solve issues within the organization and improve its performance while it’s dealing with security breaches.
- Physical security consultants keep the workplace and the machines containing classified data safe and secure.
With the help of these people, your company will get back on its feet and come out stronger and more vigilant than it was prior to the cyber attack.
- Protect yourself from future attacks.
When you’ve hired experts to help you or your company recover, it’s time to practice defending yourself from the recurrence of similar attacks.
If you keep tax data and other sensitive financial information on a computer, follow the steps below to keep your business safe from ransomware and other harmful malware:
- Disable macros in Microsoft Office files.
- Show hidden file extensions.
- Do not use Remote Desktop Protocol for file sharing.
- Block emails that contain attachments with double file extension, especially those ending in .exe.
- Scrutinize the details of the site you’re transacting on.
No matter how alike a fake page seems to be with the original site, there are some design trademarks that the scammer won’t be able to copy. Just spending a bit more time minding the URL of the site will reveal certain discrepancies that will help you determine whether you’re inputting your details on a legit or a scam site.
You don’t have to feel stuck when a financial security breach happens to you or your business. By following the tips above, your business will be able to recover in no time. And in case of another attack, you’ll be better prepared to face it head-on.




